Partnership
Private by Design: How TokenOps and Zama Are Redefining Token Distribution and Capital Formation
Mar 12, 2026
Discover how TokenOps and Zama are redefining token distribution and capital formation by combining enterprise-grade token operations with a privacy-first layer, enabling confidential vesting, airdrops, and Dutch auctions that protect strategic allocations while remaining fully verifiable on-chain.

1. Why Privacy Is the Next Crypto Supercycle
The first eight years of crypto proved Bitcoin’s viability. The next eight delivered programmability: Ethereum, DeFi, and tokenization. Balaji Srinivasan and others have argued, the coming era - privacy - arrives with urgency. With over $3.4b in 2025 theft and personal wallet theft accounting for 20% of total theft - privacy is no longer optional but existential infrastructure.
Public blockchains solved trust through radical transparency. Every transaction, every balance, every unlock event is visible. That’s great for verifiability, but not viable for all sensitive data. Token vesting schedules, payroll, strategic allocations, KOL incentive deals: in traditional finance, these are tightly controlled. On-chain, they are often broadcast to the world.
The pseudo-anonymous nature of blockchain was initially considered sufficient for privacy. However, on-chain analytics and deanonymization have proven otherwise. In practice, anyone with the right tools can reconstruct who got what, when, and on what terms. As such bold business leaders like Chamath Palihapitiya, have even predicted wider institutional adoption of a new cryptographic paradigm that is: ‘fungible, tradeable, completely secure and private’.
This is the gap TokenOps and Zama are closing: combining a battle-tested token distribution platform with a production-ready encryption layer so token auctions, pre-sales, vesting allocations, and payroll can move on-chain without exposing a project’s strategy to the entire market.
2. The Structural Problem: When Transparency Becomes a Liability
2.1 Market Manipulation Through Information Asymmetry
Public blockchains expose every transaction, balance, and vesting schedule, enabling sophisticated actors to systematically extract value from predictable events.
Comprehensive analysis of over 5,000 token unlock events by 6th Man Ventures reveals that, on average, token prices were about 13% higher 15 days before the unlock, and rose moderately after unlocks occurred. The median line showed a stronger downward trend for prices after unlock, dropping another 5%.
Figure 1 - Price Impacts From Unlocks (Source: 6MV Article)
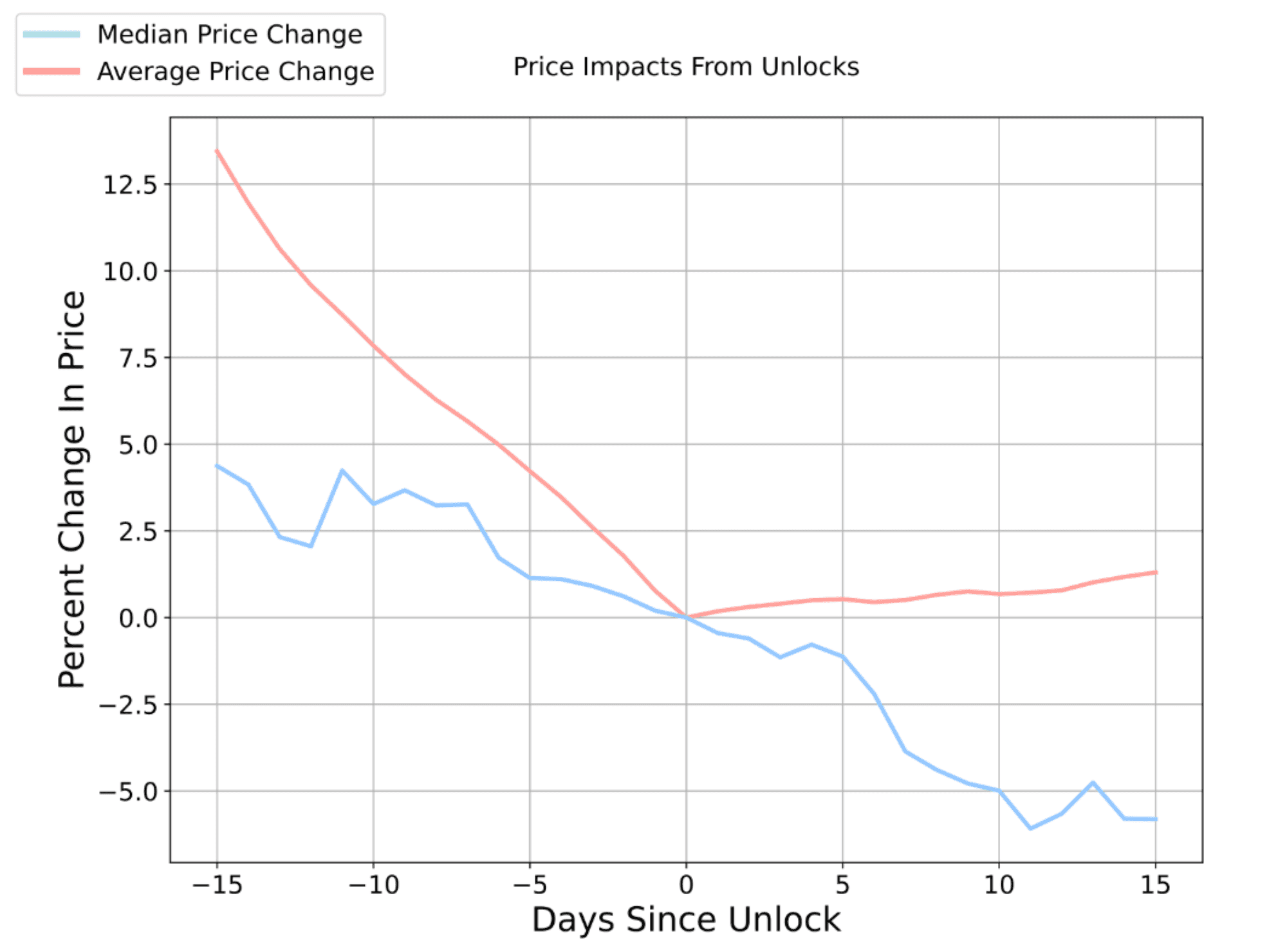
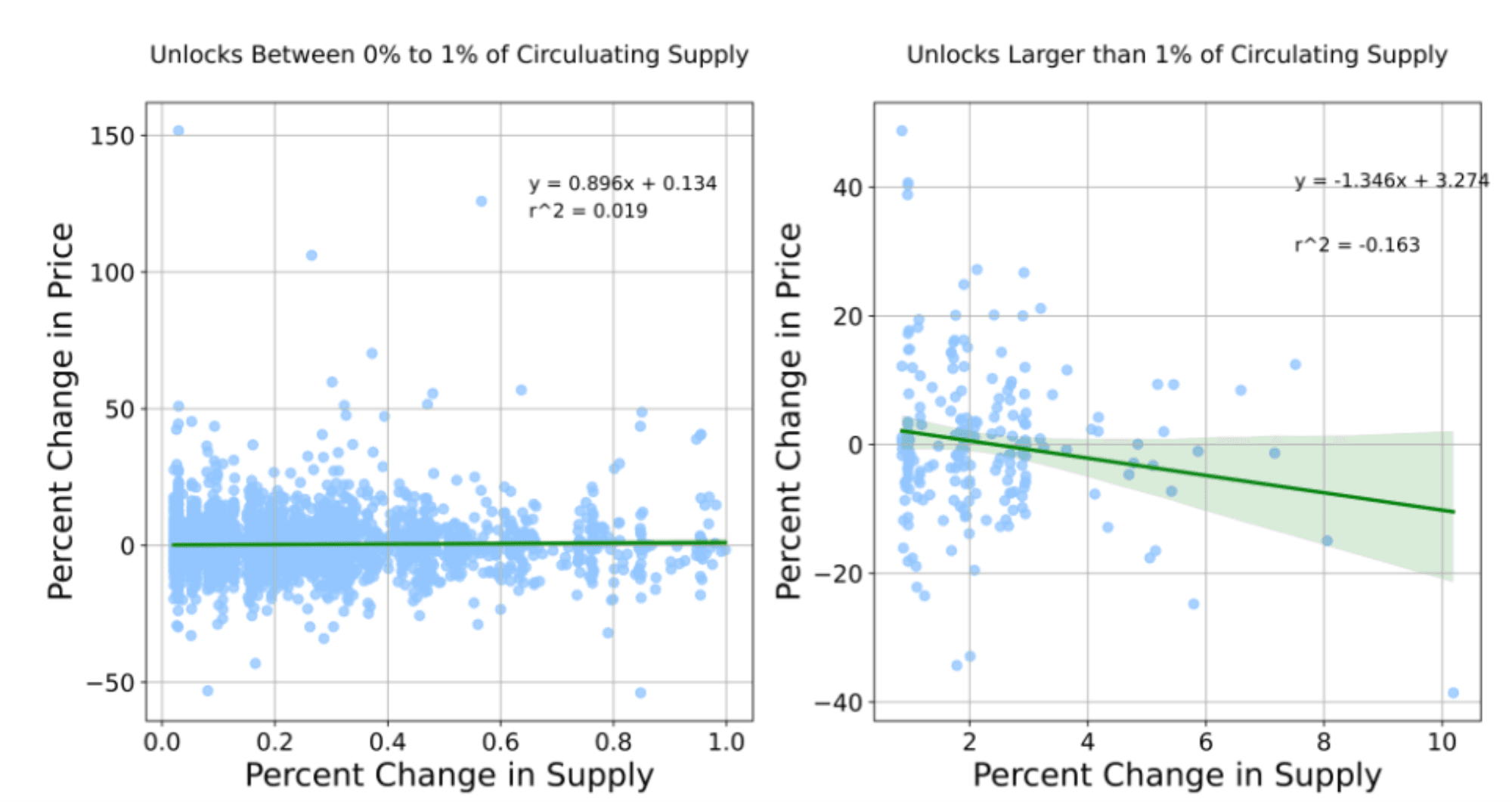
They also show unlocks exceeding 1% of circulating supply demonstrate consistent negative price correlation.Token unlock price impacts follow a predictable pattern:
0-1% of circulating supply: Negligible impact
>1% of circulating supply: -7% to -15% within 3-7 days post-unlock
Large cliff events: Up to -20% drawdowns within 15 days
Figure 2 - Unlock Size (% of Circulating Supply) vs Price Impact (Source: 6MV Article)
Substantiating the above findings, Keyrock Research findings show 90% of unlock events create negative price pressure, with impacts beginning well before actual unlock dates. Team unlocks cause price drops up to 2.4 times greater than other types due to immediate liquidation.
A recent Kaito unstaking event illustrated how visibility of large unstaking transactions triggered "run-on-the-bank" dynamics where participants rushed to the exit, creating the very selling pressure they feared.
2.2 Security Vulnerabilities and Physical Risk
The threat landscape intensified dramatically in 2025: Chainalysis reported $3.4 billion stolen across 158,000 incidents affecting 80,000+ victims, with personal wallet compromises surging from 7.3% to 44% of total stolen value ($713 million). Individual attacks tripled from 54,000 to 158,000.
Figure 3 - Anomalous Metamask Stolen Fund Events (Source: Chainanalysis Article)
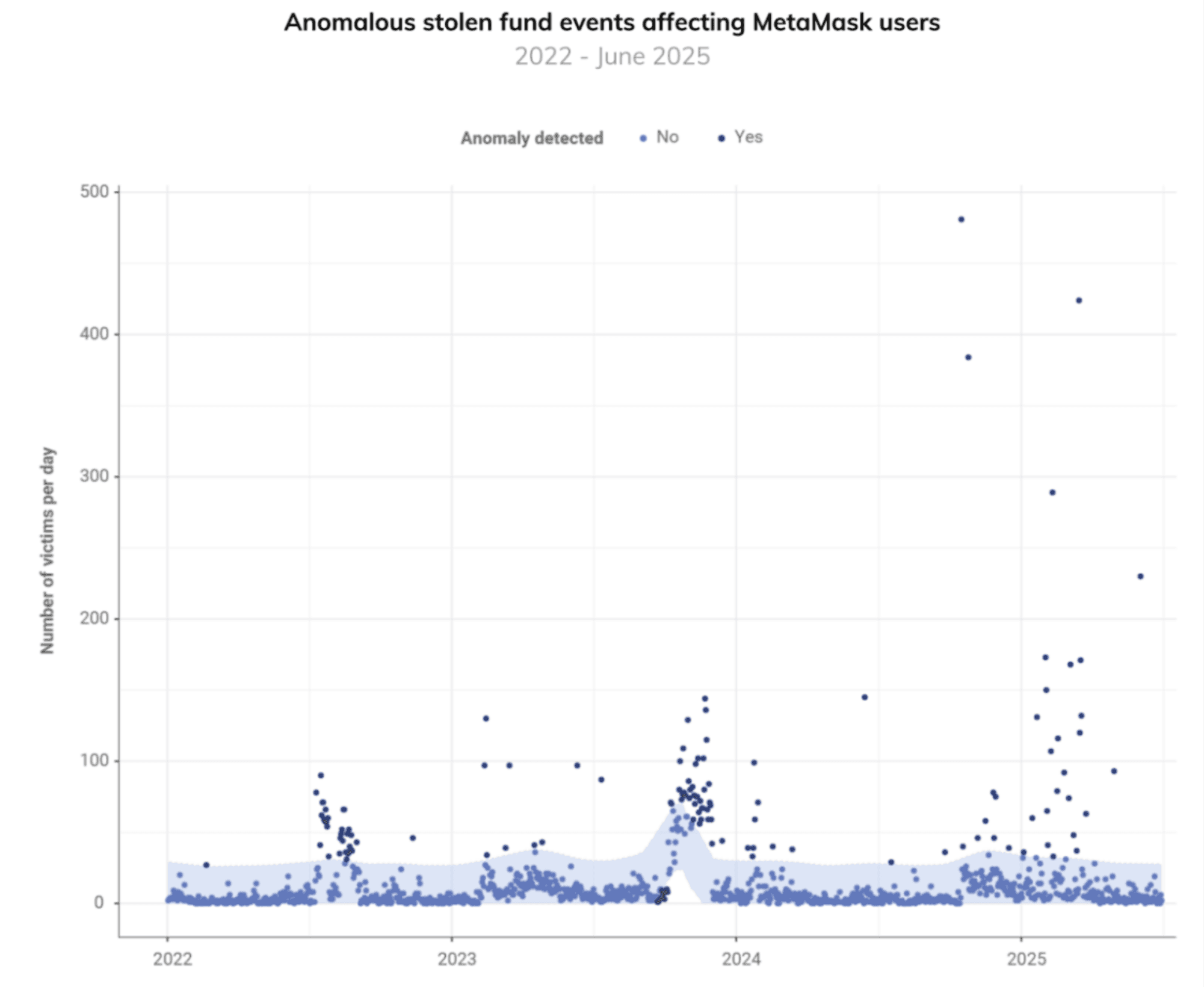
France saw a surge in physical attacks, including the abduction of Ledger co-founder David Balland. A French tax agent was indicted for extracting confidential investor records and allegedly selling them to criminals.
Neither CEXs nor public blockchains offer refuge. The Coinbase breach exposed $400 million in user data, while phishing attacks surged 40% via fake exchange sites. CEXs concentrate risk - single breaches expose thousands simultaneously.
Public blockchains fail because deanonymization eliminates pseudonymity. Arkham Intelligence uses AI to systematically deanonymize blockchain activity, linking wallets to real-world identities. Block explorers and Etherscan provide public access to wallet activity, enabling surveillance of income streams. This creates an ecosystem where transparency tools become weapons for targeted attacks.
3. Zama: A Privacy Layer for Programmable Money
3.1 FHE Architecture and Foundation
Zama delivers what institutions and enterprises require but blockchains never provided: compute on encrypted data while maintaining public verifiability - eliminating the false choice between transparency and privacy. Using Fully Homomorphic Encryption (FHE) via its fhEVM stack, Zama allows contracts to process encrypted amounts and balances without on-chain decryption, enabling confidential payroll, vesting, and treasury operations that traditional finance already expects.
In late 2025, Zama launched its protocol on Ethereum mainnet with the first ever confidential stablecoin transaction on Ethereum where amounts and balances are encrypted, yet transactions remain verifiable and final. Instead of publishing “Alice sent 1,000 tokens to Bob,” the chain records a valid encrypted transfer. Only authorized wallets can decrypt and see that it was 1,000.
Crucially, Zama is not a privacy coin, nor an L2. Rather it is a privacy layer for existing assets and protocols
ERC-7984, developed with OpenZeppelin and others, standardizes confidential fungible tokens where balances and transfers are represented as encrypted pointers.
The Ethereum network still verifies state transitions; the sensitive data itself stays encrypted.
A decentralized network of top-tier operators (including LayerZero, OpenZeppelin, and Etherscan) runs Zama’s protocol, earning Zama tokens for verifiable ciphertext computations and proofs.
Figure 4 - Zama Genesis Operator Selection (Source: Zama Blog)
3.2 Economic Model and Accessibility
Cost structure:
Base gas costs: Comparable to standard EVM transactions due to symbolic execution offloading computation to coprocessors, eliminating the privacy tax that previously made confidential operations 100x+ more expensive than transparent alternatives
Protocol fees: Paid in $ZAMA tokens to operators performing FHE computation
Layer 2 support: Deployment across Ethereum, Base, Polygon for lower-cost execution
As Total Value Shielded (TVS) grows, encryption/decryption demand increases, driving $ZAMA fee collection flowing to network operators as staking rewards and supporting token burns reducing circulating supply
4. TokenOps + Zama: Live Today, Built for the Privacy Era
TokenOps has already processed $2 billion in token distributions across 500,000+ transactions for hundreds of thousands of users. With confidential vesting integrated into Zama's FHE layer as of January 2026, this battle-tested platform now brings privacy to the token infrastructure that enterprises and institutions require.
Within the broader tokenization wave, projected to grow from roughly $1.2 trillion in 2025 to over $5.2 trillion by 2029, token operations infrastructure is the unglamorous but essential plumbing. TokenOps and Zama are not inventing a new category; they are upgrading an existing one to provide fundamental privacy rights.
The integration is live on testnet today for vesting, available for private beta testing. TokenOps has deployed a confidential vesting contract architecture that plugs into Zama’s encrypted computation layer. Upcoming modules, such as confidential presales and more sophisticated allocation mechanics, are being built on the same foundation.
The division of responsibilities is clear:
TokenOps: orchestrates token issuance, vesting, airdrops, and reporting.
Zama: encrypts the financial data inside those flows while preserving verifiability.
Projects and teams keep their familiar token operations workflows and platforms intact. Yet public blockchains’ transparent vesting hands rivals free intelligence via Etherscan - fueling smear campaigns around unlocks - while confidential vesting delivers true strategic protection.
4.1 Private Vesting
TokenOps built the confidential vesting contracts integrated with Zama's FHE. Unlike standard ERC-20 vesting - where token unlock schedules, recipient identities, and dollar amounts are broadcast to competitors via Etherscan - confidential vesting hides sensitive details while maintaining on-chain verifiability:
Originators decrypt the full state for control/compliance.
Vestees view only their own allocation/schedule.
Public observers see the contract and valid unlocks but not values or graphs.
Execution is deterministic, with standard gas fees plus affordable Zama protocol fees (in $ZAMA, volume-discounted). The same rails support confidential on-chain payroll for private recurring payments.
Figure 5 - TokenOps Claiming Portal (Source: TokenOps Claim-App)
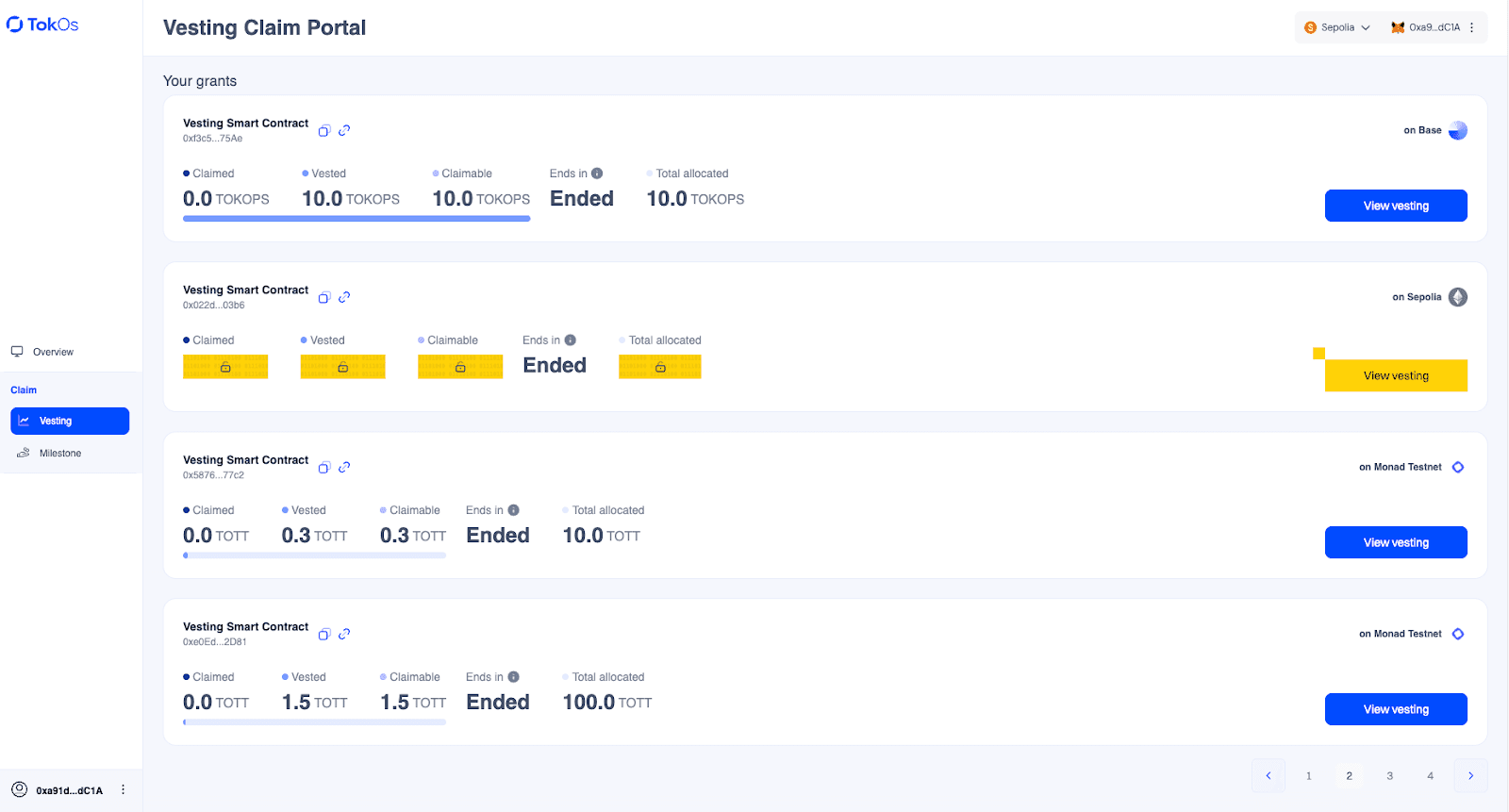
Users connect their wallet to the TokenOps claim app to view all vesting contracts where their address is a recipient. TokenOps automatically indexes the wallet across chains to surface active distributions. The above interface displays three standard vesting contracts with full transparency (allocated amounts, claimed amounts, remaining balances publicly visible) alongside one confidential vesting contract (yellow boxes) powered by Zama FHE, where key allocation data remains cryptographically obscured.
Figure 6 - Confidential Vesting Decryption (Source: TokenOps Claim-App)
Sensitive data stays encrypted until the recipient's wallet signs a decryption request through TokenOps. The frontend calls the contract with their address, triggering Zama's FHE coprocessors to use threshold MPC for selective decryption - revealing only that user's personalized amounts and timeline client-side. Observers see contract activity but cannot access values, recipient identities, or schedules.
4.2 Confidential Dutch Auction
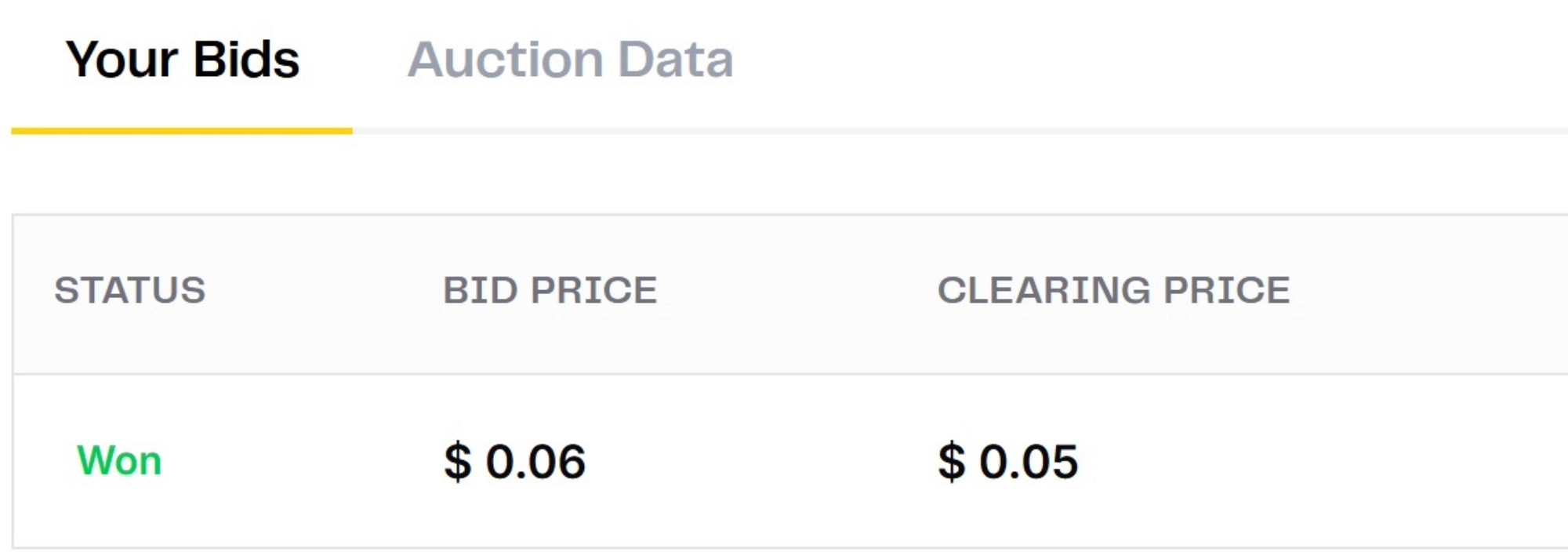
Zama's internal team built the first on-chain sealed-bid Dutch auction for the $ZAMA token sale (10-12% of supply, executed in January 2025). Bids feature public prices but confidential quantities, preventing front-running, bot sniping, gas wars, or manipulation. The clearing price is computed entirely on encrypted data for fair discovery and broad distribution. This draws from historical sealed-bid models like Google's 2004 IPO but brings true privacy on-chain.
The process of participation follows 4 simple steps:
Step 1 & 2: User verification and token shielding
Figure 7: Zama Auction Shielding Phase (Source: Zama Auction Page)
Step 2: Place and manage bids
Figure 8: Zama Auction Manage Bids Phase (Source: Zama Auction Page)
4.3 Private Airdrop
TokenOps built a confidential airdrop smart contract, audited by Open Zeppelin, for projects to distribute token en masse to their community. The airdrop meta has shifted, away for generic points campaigns to precise and targeted distributions often leveraging teams like Guild.xyz.
Eligibility, amounts, and lockups are enforced on-chain while end-to-end encrypted. Eligible addresses decrypt only their own allocation; different segments receive varied terms without exposing logic to competitors or the public. This enables fair, targeted drops to communities without stirred resentment or enabling copycat distributions by competitors.
4.4 Complementary Privacy Products
Private Staking
Confidential staking keeps individual positions, amounts, and rewards private, revealing only verifiable aggregates or final outcomes. This reduces coercion/bias in delegation, front-running in yields, and supports secure governance (private votes with only tallies shown). It fits network security use cases, like staking $ZAMA for Zama Protocol operators.
Confidential Governance
Private voting mechanisms hide individual votes and staked amounts, preventing bias, bribery, or blackmail while disclosing only the final tally. This enables secure, manipulation-resistant decision-making for DAOs, foundations, or protocols.
4.5 How It All Comes Together: Privacy Across the Project Lifecycle
These products form an integrated privacy stack that supports projects from inception through maturity:
Early Capital Formation: Confidential Dutch Auction enables fair, manipulation-resistant token raises (e.g., Zama's own sale)
Token Distribution & Incentives: Private Airdrop and Private Vesting handle community rewards, team allocations, and grants confidentially
Ongoing Operations & Network Security: Private Staking secures protocol participation while Confidential Governance supports bias-free decision-making
Long-Term Compliance & Stability: Selective decryption for auditors/regulators enables compliance with MiCA (EU), CLARITY Act (US), and emerging tokenization regulations without exposing strategies to competitors
Together, TokenOps (distribution tools) and Zama (FHE infrastructure) will enable past, present and future projects to build secure, private token economies without sacrificing blockchain transparency.
5. Market Impact and Ecosystem Benefits
5.1 Eliminating Predictable Sell-Offs & Cartel Bidding
Confidential vesting eliminates information asymmetry enabling front-running. Without visibility into unlocks, traders cannot position for anticipated selling pressure.
Market stabilization:
Unpredictable supply: No advance knowledge to model shocks, reducing pre-event positioning
Elimination of cliff drawdowns: Private linear releases distribute supply gradually without signaling
Collusion-resistant Dutch auctions: Zama’s sealed-bid encrypted auctions remove visibility of individual bids, breaking cartel formation and enabling true, fair price discovery without coordinated manipulation
5.2 Security Hardening
Encrypted balances fundamentally alter security landscape:
Physical security: Wallet holdings remain opaque, preventing high-value target identification
MEV reduction: Confidential operations reduce front-running surfaces
Untraceable wallets: Users participate without linking to historical behaviour as noted by analytics leaders Nansen privacy implications article
5.3 Organizational and Competitive Advantages
Strategic benefits:
Internal alignment: Encrypted compensation (also pioneered by Bron) prevents visibility into individual allocations, eliminating workplace/vendor tensions
Negotiating leverage: token deals remain confidential, preventing benchmarking
Regulatory compliance: Programmable privacy enables selective disclosure to regulators while maintaining confidentiality from competitors.
On-chain payroll: Organizations pay employees with only payer and payee decrypting amounts, unlocking operational efficiency without privacy sacrifice.
Grayscale's 2026 outlook emphasizes privacy is a fundamental component of the financial system, noting most people assume salary, tax information, asset size, and spending habits should not be publicly displayed.
5.4 Ecosystem Transformation
The relationship between adoption and token economics creates aligned incentives: as confidential distribution becomes standard, TVS (Total Value Shielded) grows, encryption demand increases, $ZAMA fee collection rises, flowing to operators and supporting burns reducing circulating supply.
Zama's own TGE will leverage confidential distribution, demonstrating credible commitment through self-use.
6. Closing: From “Transparent by Default” to “Confidentiality by Design”
"Over the past two years, privacy was a key customer demand that we couldn't meet effectively due to the lack of appropriate technologies in the market.
With Zama reaching mainnet, TokenOps combined with FHE technology, can eventually deliver the essential upgrade for token operations next phase: confidential vesting, presales, and capital formation that stay verifiable on-chain while protecting allocation sizes, schedules, and strategic terms from competitors and market adversaries.
FHE-based privacy is the ultimate enabler for sustainable growth of the blockchain industry, safeguarding team incentives, investor deals, and auditability.
Fabio Mancini, Co-Founder & CEO, TokenOps
"In a world of deanonymization, no project wants its internal vesting or presale terms exposed to front-runners. Zama’s fhEVM enables computation on encrypted data, keeping balances private yet provably correct. Our live integration with TokenOps powers confidential vesting today, and our $ZAMA Dutch auction - utilizing fully encrypted bids- sets a new standard for how capital formation should function: fair, private, and manipulation-resistant.
Rand Hindi, Co-Founder & CEO, Zama
6.1 Zama 2026 Roadmap
TokenOps has already secured the distribution of over $1.5 billion in assets for hundreds of thousands of users. By integrating Zama’s mainnet-ready privacy layer and adhering to new standards like ERC-7984, we are moving beyond "Privacy Coins" toward a "Privacy Layer" for the entire Ethereum ecosystem.
The shift begins this Q1. The technology is no longer theoretical - it is live:
January 21, 2026: The $ZAMA Confidential Dutch Auction went live, demonstrating the first large-scale use of encrypted price discovery.
February 2, 2026: Allocations from the Confidential Dutch Auction were claimable with bonuses sent directly to recipient wallets.
Q1 2026: General availability of Confidential Vesting and Staking for institutional partners.
6.2 The Missing Primitive for Mature Token Economies
Public blockchains made capital programmable but not governable at scale. Institutions won't deploy serious payroll, treasury operations, or strategic allocations onto fully public rails without privacy. Projects increasingly recognize that transparent token operations leak critical strategies and violate privacy as a fundamental human right.
Confidentiality is the missing primitive for mature token economies. TokenOps and Zama deliver it through production infrastructure: OpenZeppelin-audited contracts with confidential vesting live today. In 2026, the question for project leads is no longer "if" you need privacy, but "when" your competitors will make it their standard.
To see how Private by Design can protect your team's incentives and your project's market stability, book a demo with our team.
FAQs
What is confidential vesting in crypto?
Confidential vesting encrypts token amounts and schedules on‑chain so only originators and recipients see their data, while the contract still enforces unlock logic transparently.
Why is privacy now critical for token economies?
Visible vesting, payroll, and unlocks let traders front‑run supply shocks and put teams at physical and cyber risk as holdings and income streams become easy to map. Analyses of token unlocks such as CryptoRank’s research on market‑playing unlocks and industry pieces like Milk Road’s overview of Zama as a privacy upgrade highlight how transparency alone now creates structural vulnerabilities.
How do Zama and TokenOps add privacy without losing trust?
Zama’s FHE layer lets smart contracts compute on encrypted balances, and TokenOps connects this to audited vesting, airdrop, and auction contracts so workflows stay the same but numbers stay hidden. The Zama protocol overview and OpenZeppelin’s TokenOps–Zama confidential airdrop audit show how programmable privacy and formal security reviews combine for institutional‑grade token operations.
What makes a confidential Dutch auction different?
In Zama’s sealed‑bid Dutch auctions, only bid prices are public while sizes stay encrypted, stopping cartels, bots, and gas wars and still producing a single fair clearing price. Coverage of the Zama public auction and press releases like Investegate’s note on encrypted sealed‑bid auctions underline how encrypted bidding changes token sale dynamics.
How does confidential infrastructure reduce market manipulation?
By removing public unlock sizes, allocation terms, and bid quantities, speculators lose the data needed to model forced selling or copy deals, which dampens unlock dumps and coordinated auction games. Figment’s explainer on programmable privacy, “Inside Zama: How Fully Homomorphic Encryption Brings Programmable Privacy to Public Blockchains”, shows how encrypted state reshapes trading incentives at the protocol level.
